Cloud call recording applications are rising in popularity, along with cloud contact centers in general. The advantages are significant, primarily around the elimination of procuring and maintaining costly hardware, the ability to access call records from just about any web-connected device and subscription-based models. With these many cloud benefits, however, comes a heightened risk to internet-based attacks which aim to compromise your recorded calls and your private network. The emergence of mobile phone recording also adds to this ongoing security challenge.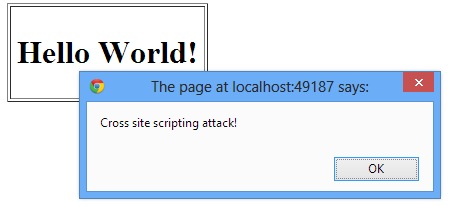
There are a number of risk-mitigation measures you can put in place, such as OWASP (Open Web Application Security Project) Level 2 security, but first you need to understand the types of threats that exist to your cloud call recording system.
“Most vulnerabilities found in the proprietary code of Web applications are unknown to security defense systems; these are called zero-day vulnerabilities. This is because these vulnerabilities are specific to each application and have never been known before. A skilled attacker can easily find these vulnerabilities and exploit the issue without being detected. The best defense against these attacks is to develop secure applications. Developers must be aware of how application attacks work and build software defenses right into their applications.
Educating and informing developers about application vulnerabilities is the goal of OWASP. The organization has put together a list of the most common application attacks. This list is renewed every three years, with the latest refresh in 2013.”
Download our white paper for descriptions of four of the most common web-based application attacks that you should be aware of in your contact center.

